Connecting Windows 10 to IPSec/L2TP on Debian 10
0
votes
1
answer
1615
views
Trying to get Windows 10 (192.168.1.11) to connect to IPSec/L2TP on Debian 10 (192.168.1.31).
Windows firewall is off and I have added 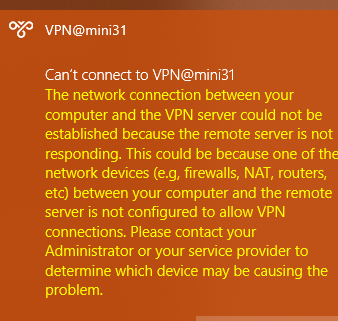 And in
And in 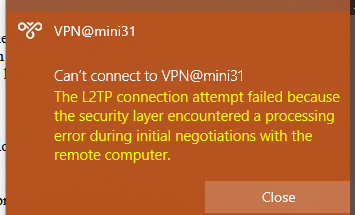
AssumeUDPEncapsulationContextOnSendRule (value 2) to the registry and rebooted.
The only iptables stuff going on on 192.168.1.31 is ip masquerade for the 192.168.1.0/24 network to the Internet.
I've got Debian set up as below and have configured the VPN in Windows with the username and password.
However Windows will not connect; an error appears in the System part of the Event Viewer which says
> The user RWB-LAPTOP-DELL\User dialed a connection named VPN@mini31 which has failed. The error code returned on failure is 809.
*/etc/ipsec.conf*
config setup
conn wep-ap
type=transport
authby=secret
pfs=no
rekey=no
keyingtries=1
left=%any
leftid=%any
right=%any
auto=add
esp=aes128-sha1-modp1536
ike=aes128-sha1-modp1536
include /var/lib/strongswan/ipsec.conf.inccharon {
plugins {
eap_dynamic {
preferred = eap-mschapv2, eap-tls
}
}
}%any %any : PSK "password"laptop * password *noccp
auth
mtu 1410
mru 1410
nodefaultroute
proxyarp
silent
debug
ms-dns 192.168.3.31[global] ; Global parameters:
port = 1701 ; * Bind to port 1701
access control = no
[lns default] ; Our fallthrough LNS definition
ip range = 192.168.3.100-192.168.3.254 ; * But this one is okay
local ip = 192.168.3.31 ; * Our local IP to use
name = mini31 ; * Report this as our hostname
pppoptfile = /etc/ppp/options.xl2tpd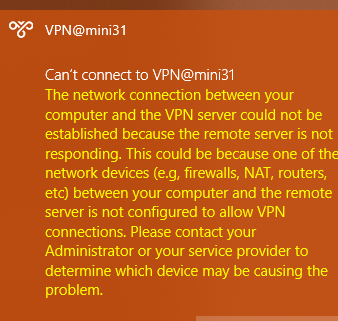 And in
And in syslog:
mini31 # cat -n syslog | tail +3203
3203 Nov 20 20:24:45 mini31 charon: 13[NET] received packet: from 192.168.1.11 to 192.168.1.31 (408 bytes)
3204 Nov 20 20:24:45 mini31 charon: 13[ENC] parsed ID_PROT request 0 [ SA V V V V V V V V ]
3205 Nov 20 20:24:45 mini31 charon: 13[ENC] received unknown vendor ID: 01:52:8b:bb:c0:06:96:12:18:49:ab:9a:1c:5b:2a:51:00:00:00:01
3206 Nov 20 20:24:45 mini31 charon: 13[IKE] received MS NT5 ISAKMPOAKLEY vendor ID
3207 Nov 20 20:24:45 mini31 charon: 13[IKE] received NAT-T (RFC 3947) vendor ID
3208 Nov 20 20:24:45 mini31 charon: 13[IKE] received draft-ietf-ipsec-nat-t-ike-02\n vendor ID
3209 Nov 20 20:24:45 mini31 charon: 13[IKE] received FRAGMENTATION vendor ID
3210 Nov 20 20:24:45 mini31 charon: 13[ENC] received unknown vendor ID: fb:1d:e3:cd:f3:41:b7:ea:16:b7:e5:be:08:55:f1:20
3211 Nov 20 20:24:45 mini31 charon: 13[ENC] received unknown vendor ID: 26:24:4d:38:ed:db:61:b3:17:2a:36:e3:d0:cf:b8:19
3212 Nov 20 20:24:45 mini31 charon: 13[ENC] received unknown vendor ID: e3:a5:96:6a:76:37:9f:e7:07:22:82:31:e5:ce:86:52
3213 Nov 20 20:24:45 mini31 charon: 13[IKE] 192.168.1.11 is initiating a Main Mode IKE_SA
3214 Nov 20 20:24:45 mini31 charon: 13[CFG] selected proposal: IKE:AES_CBC_256/HMAC_SHA1_96/PRF_HMAC_SHA1/ECP_384
3215 Nov 20 20:24:45 mini31 charon: 13[ENC] generating ID_PROT response 0 [ SA V V V V ]
3216 Nov 20 20:24:45 mini31 charon: 13[NET] sending packet: from 192.168.1.31 to 192.168.1.11 (160 bytes)
3217 Nov 20 20:24:45 mini31 charon: 14[NET] received packet: from 192.168.1.11 to 192.168.1.31 (228 bytes)
3218 Nov 20 20:24:45 mini31 charon: 14[ENC] parsed ID_PROT request 0 [ KE No NAT-D NAT-D ]
3219 Nov 20 20:24:45 mini31 charon: 14[ENC] generating ID_PROT response 0 [ KE No NAT-D NAT-D ]
3220 Nov 20 20:24:45 mini31 charon: 14[NET] sending packet: from 192.168.1.31 to 192.168.1.11 (212 bytes)
3221 Nov 20 20:24:45 mini31 charon: 15[NET] received packet: from 192.168.1.11 to 192.168.1.31 (76 bytes)
3222 Nov 20 20:24:45 mini31 charon: 15[ENC] parsed ID_PROT request 0 [ ID HASH ]
3223 Nov 20 20:24:45 mini31 charon: 15[CFG] looking for pre-shared key peer configs matching 192.168.1.31...192.168.1.11[192.168.1.11]
3224 Nov 20 20:24:45 mini31 charon: 15[CFG] selected peer config "wep-ap"
3225 Nov 20 20:24:45 mini31 charon: 15[IKE] IKE_SA wep-ap established between 192.168.1.31[192.168.1.31]...192.168.1.11[192.168.1.11]
3226 Nov 20 20:24:45 mini31 charon: 15[ENC] generating ID_PROT response 0 [ ID HASH ]
3227 Nov 20 20:24:45 mini31 charon: 15[NET] sending packet: from 192.168.1.31 to 192.168.1.11 (76 bytes)
3228 Nov 20 20:24:45 mini31 charon: 06[NET] received packet: from 192.168.1.11 to 192.168.1.31 (316 bytes)
3229 Nov 20 20:24:45 mini31 charon: 06[ENC] parsed QUICK_MODE request 1 [ HASH SA No ID ID ]
3230 Nov 20 20:24:45 mini31 charon: 06[CFG] selected proposal: ESP:AES_CBC_128/HMAC_SHA1_96/NO_EXT_SEQ
3231 Nov 20 20:24:45 mini31 charon: 06[IKE] received 3600s lifetime, configured 0s
3232 Nov 20 20:24:45 mini31 charon: 06[IKE] received 250000000 lifebytes, configured 0
3233 Nov 20 20:24:45 mini31 charon: 06[ENC] generating QUICK_MODE response 1 [ HASH SA No ID ID ]
3234 Nov 20 20:24:45 mini31 charon: 06[NET] sending packet: from 192.168.1.31 to 192.168.1.11 (188 bytes)
3235 Nov 20 20:24:45 mini31 charon: 05[NET] received packet: from 192.168.1.11 to 192.168.1.31 (60 bytes)
3236 Nov 20 20:24:45 mini31 charon: 05[ENC] parsed QUICK_MODE request 1 [ HASH ]
3237 Nov 20 20:24:45 mini31 charon: 05[IKE] CHILD_SA wep-ap{6} established with SPIs c2b5d044_i 1726a3e2_o and TS 192.168.1.31/32[udp/l2f] === 192.168.1.11/32[udp/l2f]
3238 Nov 20 20:24:46 mini31 xl2tpd: control_finish: Peer requested tunnel 3 twice, ignoring second one.
3239 Nov 20 20:24:48 mini31 xl2tpd: control_finish: Peer requested tunnel 3 twice, ignoring second one.
3240 Nov 20 20:24:52 mini31 xl2tpd: control_finish: Peer requested tunnel 3 twice, ignoring second one.
3241 Nov 20 20:25:00 mini31 xl2tpd: control_finish: Peer requested tunnel 3 twice, ignoring second one.
3242 Nov 20 20:25:10 mini31 xl2tpd: control_finish: Peer requested tunnel 3 twice, ignoring second one.
3243 Nov 20 20:25:16 mini31 xl2tpd: Maximum retries exceeded for tunnel 13486. Closing.
3244 Nov 20 20:25:16 mini31 xl2tpd: Connection 3 closed to 192.168.1.11, port 1701 (Timeout)
3245 Nov 20 20:25:20 mini31 charon: 09[NET] received packet: from 192.168.1.11 to 192.168.1.31 (76 bytes)
3246 Nov 20 20:25:20 mini31 charon: 09[ENC] parsed INFORMATIONAL_V1 request 3379181600 [ HASH D ]
3247 Nov 20 20:25:20 mini31 charon: 09[IKE] received DELETE for ESP CHILD_SA with SPI 1726a3e2
3248 Nov 20 20:25:20 mini31 charon: 09[IKE] closing CHILD_SA wep-ap{6} with SPIs c2b5d044_i (696 bytes) 1726a3e2_o (0 bytes) and TS 192.168.1.31/32[udp/l2f] === 192.168.1.11/32[udp/l2f]
3249 Nov 20 20:25:20 mini31 charon: 10[NET] received packet: from 192.168.1.11 to 192.168.1.31 (92 bytes)
3250 Nov 20 20:25:20 mini31 charon: 10[ENC] parsed INFORMATIONAL_V1 request 309590672 [ HASH D ]
3251 Nov 20 20:25:20 mini31 charon: 10[IKE] received DELETE for IKE_SA wep-ap
3252 Nov 20 20:25:20 mini31 charon: 10[IKE] deleting IKE_SA wep-ap between 192.168.1.31[192.168.1.31]...192.168.1.11[192.168.1.11]
mini31 #eap and ike**
If I use
esp=aes-sha1,3des-sha1,aes128-sha1,3des-sha1,aes128-sha256,aes128-sha1-modp1536
ike=aes-sha,3des-sha,aes128-aes256-sha1-modp3072-modp2048,3des-sha1-md5-modp1024,aes128-sha1-modp1536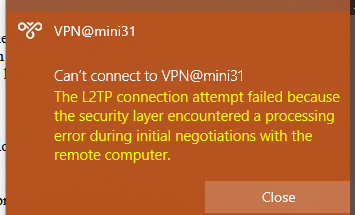
Nov 21 13:40:04 mini31 charon: 07[NET] received packet: from 192.168.1.11 to 192.168.1.31 (408 bytes)
Nov 21 13:40:04 mini31 charon: 07[ENC] parsed ID_PROT request 0 [ SA V V V V V V V V ]
Nov 21 13:40:04 mini31 charon: 07[IKE] no IKE config found for 192.168.1.31...192.168.1.11, sending NO_PROPOSAL_CHOSEN
Nov 21 13:40:04 mini31 charon: 07[ENC] generating INFORMATIONAL_V1 request 1021960079 [ N(NO_PROP) ]
Nov 21 13:40:04 mini31 charon: 07[NET] sending packet: from 192.168.1.31 to 192.168.1.11 (40 bytes)
Nov 21 13:40:05 mini31 charon: 08[NET] received packet: from 192.168.1.11 to 192.168.1.31 (408 bytes)
Nov 21 13:40:05 mini31 charon: 08[ENC] parsed ID_PROT request 0 [ SA V V V V V V V V ]
Nov 21 13:40:05 mini31 charon: 08[IKE] no IKE config found for 192.168.1.31...192.168.1.11, sending NO_PROPOSAL_CHOSEN
Nov 21 13:40:05 mini31 charon: 08[ENC] generating INFORMATIONAL_V1 request 440253701 [ N(NO_PROP) ]
Nov 21 13:40:05 mini31 charon: 08[NET] sending packet: from 192.168.1.31 to 192.168.1.11 (40 bytes)
Nov 21 13:40:06 mini31 charon: 09[NET] received packet: from 192.168.1.11 to 192.168.1.31 (408 bytes)
Nov 21 13:40:06 mini31 charon: 09[ENC] parsed ID_PROT request 0 [ SA V V V V V V V V ]
Nov 21 13:40:06 mini31 charon: 09[IKE] no IKE config found for 192.168.1.31...192.168.1.11, sending NO_PROPOSAL_CHOSEN
Nov 21 13:40:06 mini31 charon: 09[ENC] generating INFORMATIONAL_V1 request 101389495 [ N(NO_PROP) ]
Nov 21 13:40:06 mini31 charon: 09[NET] sending packet: from 192.168.1.31 to 192.168.1.11 (40 bytes)
Nov 21 13:40:09 mini31 charon: 10[NET] received packet: from 192.168.1.11 to 192.168.1.31 (408 bytes)
Nov 21 13:40:09 mini31 charon: 10[ENC] parsed ID_PROT request 0 [ SA V V V V V V V V ]
Nov 21 13:40:09 mini31 charon: 10[IKE] no IKE config found for 192.168.1.31...192.168.1.11, sending NO_PROPOSAL_CHOSEN
Nov 21 13:40:09 mini31 charon: 10[ENC] generating INFORMATIONAL_V1 request 171333823 [ N(NO_PROP) ]
Nov 21 13:40:09 mini31 charon: 10[NET] sending packet: from 192.168.1.31 to 192.168.1.11 (40 bytes)ipsec showall shows a connection, so I think the problem is with xl2tpd and in particular the Maximum retries exceeded for tunnel... Closing thing.
**Update again**
New evidence in dmesg:
[2106321.117169] audit: type=1400 audit(1611348027.206:30): apparmor="DENIED" operation="open" profile="/usr/lib/ipsec/charon" name="/proc/20839/fd/" pid=20839 comm="charon" requested_mask="r" denied_mask="r" fsuid=0 ouid=0
[2106356.184250] audit: type=1400 audit(1611348062.273:31): apparmor="DENIED" operation="open" profile="/usr/lib/ipsec/charon" name="/proc/20858/fd/" pid=20858 comm="charon" requested_mask="r" denied_mask="r" fsuid=0 ouid=0
m# aa-complain /usr/lib/ipsec/charon
Asked by Richard Barraclough
(550 rep)
Nov 20, 2020, 08:41 PM
Last activity: Apr 2, 2021, 03:07 AM
Last activity: Apr 2, 2021, 03:07 AM