How to config SSH authentication with all 3 components: publickey, password and OTP
2
votes
1
answer
480
views
**Update 1**: I'm able to apply all publickey + password + OTP with this basic config in 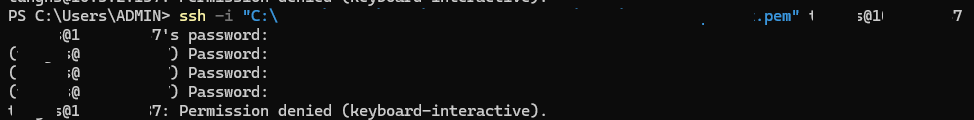 It failed in step 3 (keyboard-interactive), and some things were different from the normal OTP verification:
- It did not ask for the
It failed in step 3 (keyboard-interactive), and some things were different from the normal OTP verification:
- It did not ask for the
/etc/pam.d/common-auth.
lang-sh
auth [success=ok] pam_unix.so
auth [success=1] pam_google_authenticator.so nullok echo_verification_code [authtok_prompt=Enter your OTP:]
auth requisite pam_deny.so
auth required pam_permit.sopam_faillock.so to this as the original plan.
---------
**Original question:**
I'm using Debian 10 and 12 and would like to make my users only successfully SSH to the server if they have matched publickey, then input their password, and then follow with OTP (google-authenticator). In short, SSH should require publickey + password + OTP.
I already successfully config the combination of publickey + password or publickey + OTP, but still struggle to combine all of the three.
Please help me configure it.
My try so far:
/etc/pam.d/common-auth
lang-sh
auth required pam_faillock.so preauth audit silent deny=5 unlock_time=1800
auth sufficient pam_unix.so try_first_pass
auth [default=die] pam_faillock.so authfail audit deny=5 fail_interval=120 unlock_time=1800
auth sufficient pam_faillock.so authsucc audit deny=5 fail_interval=120 unlock_time=1800
auth required [success=1] pam_google_authenticator.so echo_verification_code
auth requisite pam_deny.so
auth required pam_permit.so/etc/pam.d/sshd
lang-sh
@include common-auth
account required pam_nologin.so
@include common-account
session [success=ok ignore=ignore module_unknown=ignore default=bad] pam_selinux.so close
session required pam_loginuid.so
session optional pam_keyinit.so force revoke
@include common-session
session optional pam_motd.so motd=/run/motd.dynamic
session optional pam_motd.so noupdate
session optional pam_mail.so standard noenv # 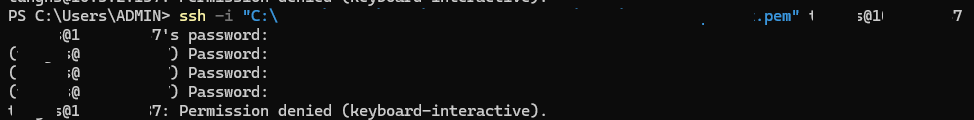 session required pam_limits.so
session required pam_env.so #
session required pam_limits.so
session required pam_env.so # 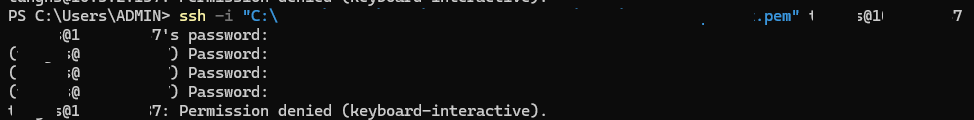 session required pam_env.so user_readenv=1 envfile=/etc/default/locale
session [success=ok ignore=ignore module_unknown=ignore default=bad] pam_selinux.so open
@include common-password
session required pam_env.so user_readenv=1 envfile=/etc/default/locale
session [success=ok ignore=ignore module_unknown=ignore default=bad] pam_selinux.so open
@include common-password/etc/ssh/sshd_config
lang-sh
Include /etc/ssh/sshd_config.d/*.conf
MaxAuthTries 5
MaxSessions 1
PubkeyAuthentication yes
PasswordAuthentication yes
PermitEmptyPasswords no
KbdInteractiveAuthentication yes
UsePAM yes
X11Forwarding yes
PrintMotd no
ClientAliveInterval 60
ClientAliveCountMax 15
AcceptEnv LANG LC_*
Subsystem sftp /usr/lib/openssh/sftp-server
ChallengeResponseAuthentication yes
AuthenticationMethods publickey,password,keyboard-interactivessh -i user@server -vvv
lang-shell
debug1: Authentications that can continue: publickey
debug3: start over, passed a different list publickey
debug3: preferred publickey,keyboard-interactive,password
debug3: authmethod_lookup publickey
debug3: remaining preferred: keyboard-interactive,password
debug3: authmethod_is_enabled publickey
debug1: Next authentication method: publickey
debug1: Trying private key:
debug3: sign_and_send_pubkey:
debug3: sign_and_send_pubkey: signing using rsa-sha2-512
debug3: send packet: type 50
debug2: we sent a publickey packet, wait for reply
debug3: receive packet: type 51
Authenticated with partial success.
debug1: Authentications that can continue: password
debug3: start over, passed a different list password
debug3: preferred publickey,keyboard-interactive,password
debug3: authmethod_lookup password
debug3: remaining preferred: ,keyboard-interactive,password
debug3: authmethod_is_enabled password
debug1: Next authentication method: password
user@server's password:
debug3: send packet: type 50
debug2: we sent a password packet, wait for reply
debug3: receive packet: type 51
Authenticated with partial success.
debug1: Authentications that can continue: keyboard-interactive
debug3: start over, passed a different list keyboard-interactive
debug3: preferred publickey,keyboard-interactive,password
debug3: authmethod_lookup keyboard-interactive
debug3: remaining preferred: password
debug3: authmethod_is_enabled keyboard-interactive
debug1: Next authentication method: keyboard-interactive
debug2: userauth_kbdint
debug3: send packet: type 50
debug2: we sent a keyboard-interactive packet, wait for reply
debug3: receive packet: type 60
debug2: input_userauth_info_req: entering
debug2: input_userauth_info_req: num_prompts 1
(user@server) Password:
debug3: send packet: type 61
debug3: receive packet: type 51
debug1: Authentications that can continue: keyboard-interactive
debug2: userauth_kbdint
debug3: send packet: type 50
debug2: we sent a keyboard-interactive packet, wait for reply
debug3: receive packet: type 60
debug2: input_userauth_info_req: entering
debug2: input_userauth_info_req: num_prompts 1
(user@server) Password:
debug3: send packet: type 61
debug3: receive packet: type 51
debug1: Authentications that can continue: keyboard-interactive
debug2: userauth_kbdint
debug3: send packet: type 50
debug2: we sent a keyboard-interactive packet, wait for reply
debug3: receive packet: type 60
debug2: input_userauth_info_req: entering
debug2: input_userauth_info_req: num_prompts 1
(user@server) Password:
debug3: send packet: type 61
debug3: receive packet: type 51
debug1: Authentications that can continue: keyboard-interactive
debug2: we did not send a packet, disable method
debug1: No more authentication methods to try.
user@server: Permission denied (keyboard-interactive).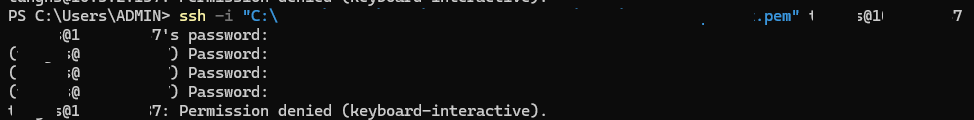 It failed in step 3 (keyboard-interactive), and some things were different from the normal OTP verification:
- It did not ask for the
It failed in step 3 (keyboard-interactive), and some things were different from the normal OTP verification:
- It did not ask for the Verification code: but just asked (user@server) Password:.
- It did not show the raw OTP code when I inputted despite config echo_verification_code in common-auth.
P/s: I also configured pam_faillock.so to lockout users for failed login attempts.
Asked by TungNS
(21 rep)
Apr 19, 2024, 03:46 AM
Last activity: Apr 22, 2024, 06:57 AM
Last activity: Apr 22, 2024, 06:57 AM